Copyright © 1996-2024 Balasys IT Zrt. (Private Limited Company)
Copyright © 2024 Balasys IT Zrt. All rights reserved. This document is protected by copyright and is distributed under licenses restricting its use, copying, distribution, and decompilation. No part of this document may be reproduced in any form by any means without prior written authorization of Balasys.
This documentation and the product it describes are considered protected by copyright according to the applicable laws.
This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit (http://www.openssl.org/). This product includes cryptographic software written by Eric Young (eay@cryptsoft.com)
Linux™ is a registered trademark of Linus Torvalds.
Windows™ 10 is registered trademarks of Microsoft Corporation.
The Balasys™ name and the Balasys™ logo are registered trademarks of Balasys IT Zrt.
The Zorp™ name and the Zorp™ logo are registered trademarks of Balasys IT Zrt.
AMD Ryzen™ and AMD EPYC™ are registered trademarks of Advanced Micro Devices, Inc.
Intel® Core™ and Intel® Xeon™ are trademarks of Intel Corporation or its subsidiaries in the U.S. and/or other countries.
All other product names mentioned herein are the trademarks of their respective owners.
DISCLAIMER
Balasys is not responsible for any third-party websites mentioned in this document. Balasys does not endorse and is not responsible or liable for any content, advertising, products, or other material on or available from such sites or resources. Balasys will not be responsible or liable for any damage or loss caused or alleged to be caused by or in connection with use of or reliance on any such content, goods, or services that are available on or through any such sites or resources.
May 30, 2024
Abstract
This document describes how to install and configure the Zorp Authentication Agent.
Table of Contents
- Summary of changes
- 1. Introduction
- 2. Authentication and Zorp
- 3. Installing the Zorp Authentication Agent (ZAA)
- 4. Configuring Zorp Authentication Agent (ZAA)
- 4.1. Configuring Zorp Authentication Agent on Microsoft Windows platforms
- 4.1.1. Registry entries on Microsoft Windows platforms
- 4.1.2. Command line parameters on Microsoft Windows platforms
- 4.1.3. Configuring SSL connections on Microsoft Windows platforms
- 4.1.4. Configuring X.509 certificate based authentication on Microsoft Windows platforms
- 4.1.5. Configuring Group Policy Object (GPO) deployment
- 4.2. Configuring ZAA on Linux platforms
- 5. Using the Zorp Authentication Agent (ZAA)
- 6. Configuring Zorp Authentication Agent preferences
- 7. Starting and stopping Zorp Authentication Agent
List of Procedures
- 2.2. Outband authentication with Zorp
- 3.1.1. Installing the Zorp Authentication Agent on Microsoft Windows
- 3.1.2. Installing Zorp Authentication Agent with Group Policy Object (GPO) deployment
- 3.2. Installing Zorp Authentication Agent on Linux platforms
- 4.1.3.1. Encrypting the communication between Zorp and the Zorp Authentication Agent on Microsoft Windows platforms
- 4.1.3.2. Importing the CA certificate manually
- 4.1.3.3. Importing the CA certificate using Microsoft Management Console (MMC)
- 4.1.4. Configuring X.509 certificate based authentication on Microsoft Windows platforms
- 4.1.5. Configuring Group Policy Object (GPO) deployment
- 4.2.2.1. Encrypting the communication between Zorp and the Zorp Authentication Agent on Linux platforms
The following changes have been made to the document between releases Zorp 7.0.18 and Zorp 7.0.19:
| Description of the change | Place in the document |
|---|---|
The information on which platform ZAA can be installed on has been updated. |
For the changes, see Chapter 3, Installing the Zorp Authentication Agent (ZAA). |
Table 1. Summary of changes
The following changes have been made to the document between releases Zorp 7.0.17 and Zorp 7.0.18:
| Description of the change | Place in the document |
|---|---|
The procedures for installing and configuring Zorp Authentication Agent with Group Policy Object (GPO) deployment have been added to the document. |
See sections Procedure 3.1.2, Installing Zorp Authentication Agent with Group Policy Object (GPO) deployment and Procedure 4.1.5, Configuring Group Policy Object (GPO) deployment. |
Zorp Authentication Agent installer options have been added to the document. |
See section Procedure 3.1.1, Installing the Zorp Authentication Agent on Microsoft Windows. |
Table 2. Summary of changes
The following changes have been made to the document between releases Zorp 7.0.15 and Zorp 7.0.16:
| Description of the change | Place in the document |
|---|---|
During authentication, Zorp Authentication Agent requires TLS-encrypted communication from Zorp. |
See sections Section 4.1.3, Configuring SSL connections on Microsoft Windows platforms and Section 4.2.2, Configuring SSL connections on Linux platforms |
Editorial changes have been made throughout the document. |
Table 3. Summary of changes
The following changes have been made to the document between releases Zorp 7.0.13 and Zorp 7.0.14:
| Description of the change | Place in the document |
|---|---|
The steps have been improved and the figures have been exchanged for a more coherent look. |
For the changes, see sections:
|
Table 4. Summary of changes
Developed by Balasys, Zorp Authentication Agent (ZAA) is an authentication client, capable of cooperating with the Zorp firewall and the Zorp Authentication Server (ZAS) to identify the users initiating network connections. Zorp Authentication Agent enables the complete network traffic to be audited on the user level.
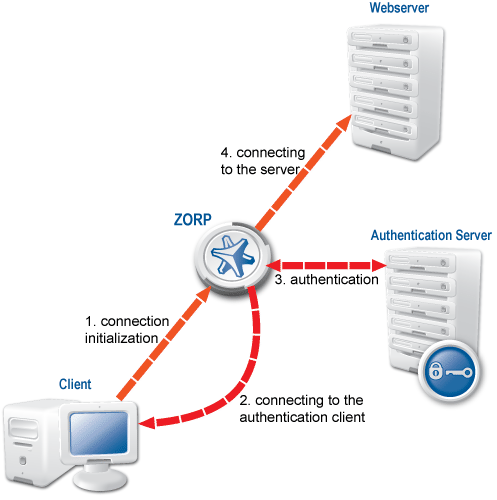
Zorp Authentication Agent (ZAA) is an authentication client, capable of cooperating with the Zorp firewall and the Zorp Authentication Server (ZAS) to identify the users initiating network connections. The authentication process and the related communication between the components is summarized below. For more details, see Chapter 15, Connection authentication and authorization in Zorp Professional 7 Administrator Guide.
The authentication aims to determine the identity of the user. During the authentication process the user initiating the connection shares a piece of sensitive information (for example, a password) with the other party that verifies the user's authenticity.
Several procedures (so called authentication methods) exist for verifying the identity of the user:
The user owns some pieces of sensitive information, for example, a password, PIN code, the response to a challenge, and so on.
The user owns a device, for example, a hardware key, chipcard, SecurID token, and so on.
Naturally, the above methods can be combined to implement strong two-factor level authentication in sensitive environments.
The aim of network authentication is to authenticate the connections initiated by the users in order to ensure that only the proper users can access the services. Basically there are two types of authentication:
Inband: Authentication is performed by the application-level protocol — the data traffic required for the authentication is part of the protocol. Inband authentication is used for example in the HTTP, FTP, or SSH protocols. The protocols usually support different authentication methods — these are usually described in the specifications of the protocol.
Outband: Authentication is performed in a separate data channel completely independent from the protocol of the accessed service. Outband authentication is realized by the combination of the Zorp Authentication Agent (ZAA), Zorp Authentication Server (ZAS), and Zorp softwares. The advantage of outband authentication is that it can be used to authenticate any protocol, regardless of the authentication methods supported by the original protocol. That way, strong authentication methods (for example, chipcards) can be used to authenticate protocols supporting only the weak username/password method (for example, HTTP).
2.2. Procedure – Outband authentication with Zorp
Purpose:
Zorp implements outband authentication according to the following procedure:
Steps:
The client initiates a connection towards the server.
Zorp determines the service to be accessed based on the IP address of the client and the server. If authentication is required for the connection (an authentication policy is assigned to the service), Zorp initiates a connection towards the client using the Zorp Authentication Agent protocol.
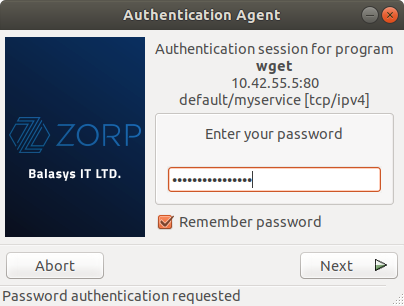
Depending on the authentication methods available (for example, for password-based authentication), the dialog of the Zorp Authentication Agent is displayed on the client machine. The user enters the username that the Zorp Authentication Agent forwards to Zorp.
The Zorp firewall connects to Zorp Authentication Server (ZAS) and retrieves the list of authentication methods enabled for the particular user. Multiple authentication methods can be enabled for a single user (for example, x509, Kerberos, password, and so on). The authorization of the user is also performed in this step, for example, the verification of the LDAP group membership.
Zorp returns the list of available methods to the client. The user selects a method and provides the information (for example, the password) required for the method.
The Zorp Authentication Agent sends the data (for example, the password) to Zorp that forwards it to ZAS.
ZAS performs the authentication and notifies Zorp about the result (success/failure).
Zorp returns the result to the client and — if the authentication was successful, builds a connection towards the server. In case of a failed authentication it terminates the connection to the client.
This section describes the installation and configuration of the Zorp Authentication Agent on Microsoft Windows and Linux platforms. The Zorp Authentication Agent has to be installed on every computer having access to authenticated services. The following platforms are supported:
Windows 10 or later (x86, x64)
Ubuntu 18.04 Bionic Beaver (64-bit only)
The agent has two components:
Zorp Authentication Agent Multiplexer: It is a daemon running in the background, accepting the connections coming from Zorp and verifying the SSL certificates of Zorp (if the communication is encrypted). In a multi-user environment the Multiplexer displays the dialog of the Zorp Authentication Agent on the desktop of the user initiating a connection requiring authentication.
Zorp Authentication Agent: This application collects the information required for the authentication, for example, the username, authentication method, password, and so on.
The installers automatically install both components. The components require approximately 10 MB of free hard disk space.
3.1.1. Procedure – Installing the Zorp Authentication Agent on Microsoft Windows
Purpose:
The Zorp Authentication Agent (ZAA) installer is located in the \windows\satyr\ folder of the Zorp CD-ROM, its latest version is also available from the Balasys website.
The following Zorp Authentication Agent installer options are available:
/S Silent mode /D=[path] Set target path /NO_VCREDIST Do not check/install Visual Studio Redistributable /log-mpxd=[yes|no] Enable debug logging of AA multiplexer daemon /log-client=[yes|no] Enable debig logging of AA client
Steps:
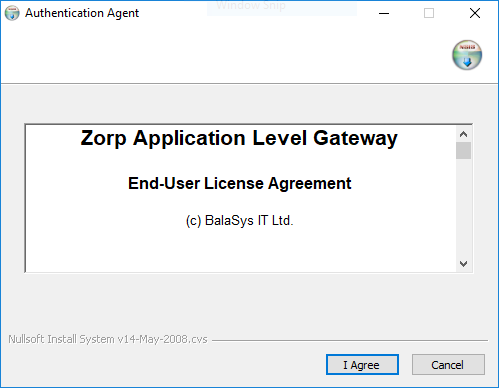
-
Place the Zorp CD-ROM into the CD drive and start the
satyr-setup.exefile located in the\windows\satyr\folder.Warning Administrator privileges are required to install the application.
-
Click to accept the End-User License Agreement, which is displayed after the installer starts. To cancel the installation at any time during the process, click .
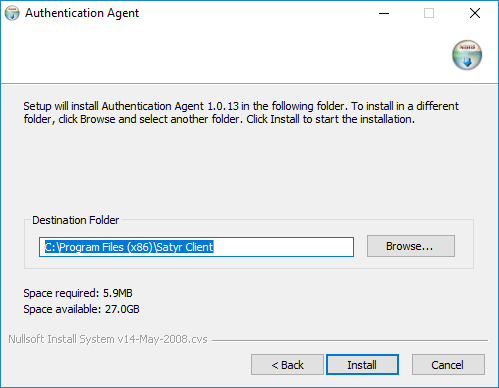
-
Select the destination folder for the application and click . The default folder in the 64-bit version of Windows is
C:\Program Files (x86)\Satyr Client(in the 32-bit version of Windows, it isC:\Program Files\Satyr Client).
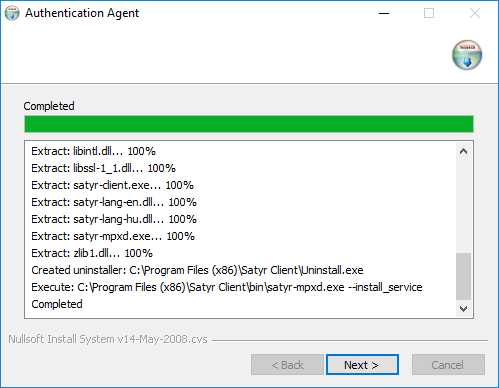
-
Click to display details about the copied files. The installer copies the required files and registers the service called , which is started after the registration.
-
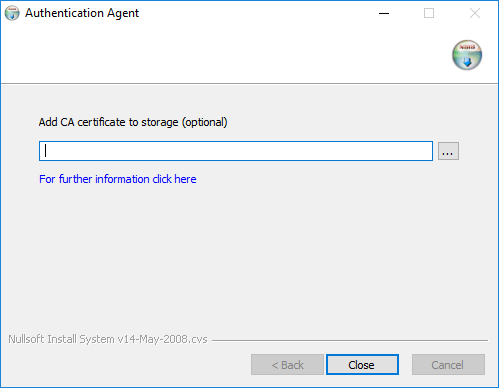
Optional step: Click , select the CA certificate to import, then click to import the CA certificate.
Note For authentication purposes, when Zorp communicates with ZAA, ZAA expects TLS-encrypted communication. For details, see section Section 4.1.1, Registry entries on Microsoft Windows platforms and section Section 4.1, Configuring Zorp Authentication Agent on Microsoft Windows platforms.
If the Zorp Authentication Agent and Zorp communicate through an SSL-encrypted channel (recommended), the certificate of the Certificate Authority (CA) signing the certificates of the Zorp firewalls can be imported to the Zorp Authentication Agent.
Note The CA certificate has to be in
DERformat. It is not necessary to import the certificate during the installation, it can also be done later. For details about encrypting the agent-Zorp authentication, see Section 4.1.3, Configuring SSL connections on Microsoft Windows platforms.
After the installer has completed the above steps, click .
The Zorp Authentication Agent (ZAA) logo is displayed on the system tray, indicating that the application is running. It is also started automatically after each Windows startup.
3.1.2. Procedure – Installing Zorp Authentication Agent with Group Policy Object (GPO) deployment
Prerequisites:
Create the necessary certificates as instructed in the Zorp Professional Administrator Guide in section Procedure 11.3.8.2, Creating certificates in Zorp Professional 7 Administrator Guide.
Set the parameters for the ZAS certificate.
Export the CA certificate signed by ZAS in .der format for the Windows client.
Steps:
Download the .exe format installer. The browser application or the Windows Defender Cloud might send a notification or a warning due to the new and unknown installer program, this can be disregarded.
Install the Windows Client and import the CA certificate during the installation. Reboot the system, if it is necessary.
Define the preferences with the help of the GUI or via the registry.
Test the expected behaviour by initiating traffic.
-
Export the following registries:
-
Export the
HKEY_CURRENT_USER\Software\BalaBit\Satyrregistry to the hlcuzaa.reg file, which contains the user settings for ZAA. The result shall be as follows:Windows Registry Editor Version 5.00 [HKEY_CURRENT_USER\Software\BalaBit] [HKEY_CURRENT_USER\Software\BalaBit\Satyr] "Has preferences"=dword:00000000 "SSL"=dword:00000001 "Automatic"=dword:00000001 "Details"=dword:00000000 "Can Remember"=dword:00000001 "Forget Password"=dword:00000000 "Forget Password Interval"=dword:00000001
-
As ZAA Client is 32 bit executable, and runs on both 32 and 64 bit systems, if the target system is a 32 bit system, as Windows, for example, the following solution is required:
Export the
HKEY_LOCAL_MACHINE\SOFTWARE\BalaBit\Satyr, which contains the ZAA Multiplexer settings, into the hklmzaa32.reg file. The result shall be as follows:Windows Registry Editor Version 5.00 [HKEY_LOCAL_MACHINE\SOFTWARE\BalaBit] [HKEY_LOCAL_MACHINE\SOFTWARE\BalaBit\Satyr] "InstallLang"="1033"
-
If the target system is a 64 bit system, export the
HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\BalaBit\Satyrregistry to the hklmzaa64.reg file, which contains the multiplexer settings. The result shall be as follows:Windows Registry Editor Version 5.00 [HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\BalaBit] [HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\BalaBit\Satyr] "InstallLang"="1033"
Note If the ZAA Client will be used on both 32 and 64 bit systems, create both registries, adding or removing the WOW6432NODE string to the paths. ZAA will use the corresponding one.
For more details, see 32-bit and 64-bit Application Data in the Registry.
Later at the deployment, the registries can be distributed as duplicated keys on the target system safely, as detailed at the following site: Registry key WOW6432Node may be listed in system registry in 32 bit (x86) version of Windows 7.
The service private certificate store, used by the ZAA Multiplexer, can also be deployed as a registry key.
-
Export the
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\ Cryptography\Services\satyr-mpxdregistry to the hklmzaacert.reg file. The result shall be as follows:Windows Registry Editor Version 5.00 [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\Services\satyr-mpxd] [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\Services\satyr-mpxd\ SystemCertificates] [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\Services\satyr-mpxd\ SystemCertificates\MY] [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\Services\satyr-mpxd\ SystemCertificates\MY\Certificates] [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\Services\satyr-mpxd\ SystemCertificates\MY\Certificates\6421DCB8501C2E1F15DB8BD3A94F435C01DB7CD3] "Blob"=hex:03,00,00,00,01,00,00,00,14,00,00,00,64,21,dc,b8,50,1c,2e,1f,15,db,\ ... ... ... ... ... 64,0a,87,e9,45,99,04,9e,28,cb,c0,6c,2a,e5,c7,cb,ce,29,d8,b1,e1
Note Note that there can be several empty paths created by the system automatically, which can be included safely.
For further details on registries, see Section 4.1.1, Registry entries on Microsoft Windows platforms.
As a result, there will be four registries exported.
-
Switch to the GPO administrator system and download the ZAA
msi flavorinstaller and place it in the Windows share where the other remotely installled applications are stored.Continue with the procedures detailed in section Procedure 4.1.5, Configuring Group Policy Object (GPO) deployment
3.2. Procedure – Installing Zorp Authentication Agent on Linux platforms
Purpose:
This section describes the installation of the Zorp Authentication Agent on Ubuntu Linux operating systems.
Steps:
-
Create a mount point for the Zorp installation medium:
sudo mkdir -p /media/cdrom
-
Mount the Zorp installation medium to the previous mount point.
sudo mount /dev/cdrom /media/cdrom -o ro
-
Install the Balasys Gnu Privacy Guard (GPG) keys to allow the checking of Zorp package signatures by APT.
sudo /media/cdrom/install-balasys-archive-key.sh
-
Make sure the following details are added as follows:
-
Add the following lines to the
/etc/apt/auth.conf.d/satyr.conffile:machine apt.balasys.hu login {your username} password {your password} -
Also limit the permissions:
chmod 600 /etc/apt/auth.conf.d/satyr.conf
-
Add the following lines to
/etc/apt/sources.list.d/zorp.listdeb https://apt.balasys.hu/zorp-os ubuntu-bionic/zorp-7.0latest satyr
-
-
Install the Zorp Authentication Agent. Issue the following commands as root:
apt update apt install satyr
The above commands install the
satyr(Zorp Authentication Agent) and thesatyr-mpxd(Zorp Authentication Agent Multiplexer) packages. Zorp Authentication Agent Multiplexer is automatically started after the installation. It can be stopped or started by issuing the
systemctl stop satyr-mpxdorsystemctl start satyr-mpxdcommands, respectively.Zorp Authentication Agent is launched on desktop environment startup. It can be started manually by running
satyr-gtk.
Some settings of Zorp Authentication Agent (ZAA) can be modified through the Windows Registry. Launch the registry editor by issuing the regedit command (either from a command prompt or through the button).
In the 64-bit version of the Registry Editor, the Zorp Authentication Agent parameters, as the parameters of a 32-bit program, are located under: HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\BalaBit\Satyr for the Multiplexer and HKEY_CURRENT_USER\Software\BalaBit\Satyr for the Client application.
The component has to be restarted if a value is modified (that is, the service for Zorp Authentication Agent Multiplexer, the Authentication Client application for Zorp Authentication Agent).
To restart the Zorp Authentication Agent Multiplexer, select the button, type and then press . Select on the list, then it.
The following settings are available from the registry:
The following table presents the settings available from the HKEY_CURRENT_USER\Software\BalaBit\Satyr registry for the Client application.
|
HKEY_CURRENT_USER\Software\BalaBit\Satyr | ||
|---|---|---|
|
Name |
Description |
Default value |
|
|
To enable the automatic Kerberos authentication without user interaction with the Zorp Authentication Agent, set it to |
|
|
|
To save your credentials so that the client will fill the username and password automatically for later authentication attempts, set this parameter to |
|
|
|
The Zorp Authentication Agent displays the details of the connection in the popup dialog if this parameter is set to |
|
|
|
To store the authentication password indefinitely in the Zorp Authentication Agent, set this parameter to |
|
|
|
To prevent unauthorized initiation of network connections through unattended machines, configure this parameter. Enter the number of minutes after which Zorp Authentication Agent deletes the stored password and requires authentication for new connection requests. |
|
|
|
To enable the menu item in the system tray icon of Zorp Authentication Agent, set this parameter to |
|
|
|
It marks the verbosity level of the authentication client, ranging from The log file is stored in the user's home directory. |
|
|
|
The installer generates it. |
|
Table 4.1. Registry setting options for the Client application
The following table presents the settings available from the HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\BalaBit\Satyr registry in the 64 bit system and from the HKEY_LOCAL_MACHINE\SOFTWARE\BalaBit\Satyr registry in the 32 bit system for the Multiplexer.
|
HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\BalaBit\Satyr (64 bit system) HKEY_LOCAL_MACHINE\SOFTWARE\BalaBit\Satyr (32 bit system) | ||
|---|---|---|
|
Name |
Description |
Default value |
|
|
This is the name and path (for example, |
string |
|
|
It is the verbosity level of the Zorp Authentication Agent Multiplexer, ranging from The log file is stored in the |
|
|
|
To configure the Zorp Authentication Agent Multiplexer so that it uses only SSL-encrypted connections, set this parameter to |
|
|
|
It is the maximum length of the verification chain. |
|
Table 4.2. Registry setting options for the Multiplexer
To display the version number of the client, enter satyr-client.exe --version.
The Zorp Authentication Agent Multiplexer (satyr-mpxd.exe) has the following command line options:
- --install_service
It registers the Zorp Authentication Agent service.
- --remove_service
It removes the Zorp Authentication Agent service.
- --start_service
It starts the Zorp Authentication Agent service.
- --stop_service
It stops the Zorp Authentication Agent service.
Zorp Authentication Agent Multiplexer and Zorp can communicate through an SSL-encrypted channel. For this, a certificate has to be available on the Zorp firewall that Zorp uses to authenticate the connection to the Zorp Authentication Agent Multiplexer. The Zorp Authentication Agent Multiplexer verifies this certificate using the certificate of the CA issuing Zorp's certificate, therefore the certificate of the CA has to be imported to the machine running the Zorp Authentication Agent.
| Note |
|---|
During authentication, when Zorp communicates with ZAA, ZAA expects TLS-encrypted communication. In order to disable this and to use the communication without encryption (which is strongly against the recommendation, but useful for debugging purposes), the SSL encryption shall be disabled by setting the SSL registry key to value '0'. For details on this parameter, see Section 4.1, Configuring Zorp Authentication Agent on Microsoft Windows platforms. Also see, Procedure 3.1.1, Installing the Zorp Authentication Agent on Microsoft Windows. |
| Note |
|---|
It is highly recommended to encrypt the communication between Zorp and the Zorp Authentication Agent, because without it, anyone can connect to the Zorp Authentication Agent Multiplexer, resulting in the authentication information obtained by unauthorized people. It is essential to use encryption when password authentication is used. For details on encryption, see Procedure 3.1.1, Installing the Zorp Authentication Agent on Microsoft Windows. |
4.1.3.1. Procedure – Encrypting the communication between Zorp and the Zorp Authentication Agent on Microsoft Windows platforms
Purpose:
To enable encryption between Zorp and the Zorp Authentication Agent, complete the following steps. For the steps to be completed from Zorp Management Console (ZMC), see Chapter 11, Key and certificate management in Zorp in Zorp Professional 7 Administrator Guide.
Steps:
Create a CA (for example,
ZAA_CA) using the Zorp Management Console (ZMC). This CA will be used to sign the certificates shown by the Zorp firewalls to the Authentication Agents.Export the CA certificate into
DERformat.-
Generate certificate request(s) for the Zorp firewall(s) and sign it with the CA created in Step 1.
Note Each firewall shall have its own certificate. Do not forget to set the firewall as the Owner host of the certificate.
Distribute the certificates to the firewalls.
-
Install the Zorp Authentication Agent (ZAA) application to the workstations and import to each machine the CA certificate exported in Step 2.
There are three ways to import the CA certificate:
Import the CA certificate by using the installer of the Zorp Authentication Agent.
Import the CA certificate manually by using the addcert and getcert programs (see Procedure 4.1.3.2, Importing the CA certificate manually).
You can also import the CA certificate by using the Microsoft Management Console (see Procedure 4.1.3.3, Importing the CA certificate using Microsoft Management Console (MMC)).
Create the appropriate outband authentication policies in ZMC and reference them among the services of Zorp. See Chapter 15, Connection authentication and authorization in Zorp Professional 7 Administrator Guide for details.
4.1.3.2. Procedure – Importing the CA certificate manually
Procedure:
To import the certificate of the CA using the addcert and getcert programs, complete the following steps.
Steps:
-
The certificate can be imported using the
addcert.exeprogram located in the installation folder of the Zorp Authentication Agent (C:\Program Files\Satyr clientby default). The program can be started from a command prompt. Provide the name and the path of theDER-format certificate as an input parameter, for example:-
On 64 bit:
C:\Program Files (x86)\Satyr Client\bin\addcert.exe C:\temp\AuthenticationAgent_CA.crt
-
On 32 bit:
C:\Program Files\Satyr Client\bin\addcert C:\tmp\AuthenticationAgent_CA.crt
Note Running
addcert.exerequires administrator privileges. -
Verify that the certificate has been successfully imported by running getcert.exe. Running getcert.exe lists the Subject of all imported certificates.
Restart the service.
4.1.3.3. Procedure – Importing the CA certificate using Microsoft Management Console (MMC)
Purpose:
To import the certificate of the CA complete the following steps.
Steps:
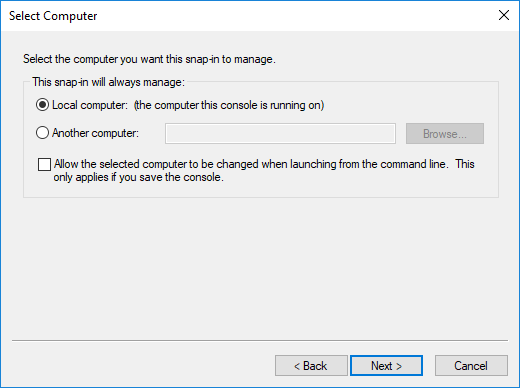
-
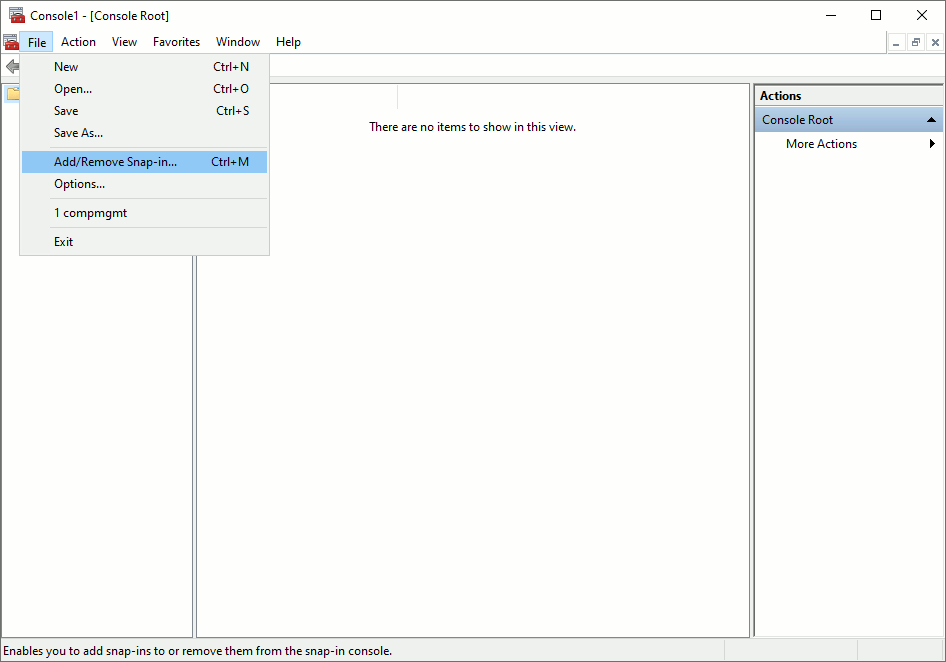
Start Microsoft Management Console by executing
mmc.exeafter selecting the button.Note Running
mmc.exerequires administrator privileges. -
Select , from the menu.
-
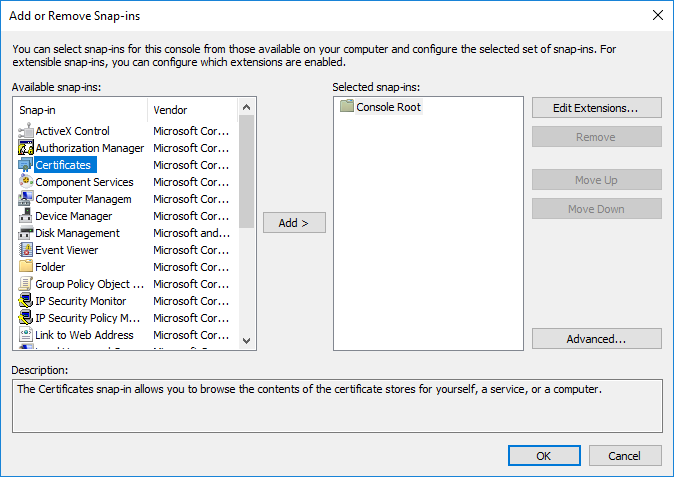
Select and click from the list.
-
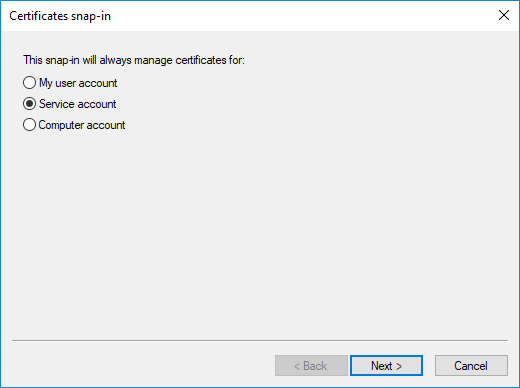
Select and click .
-
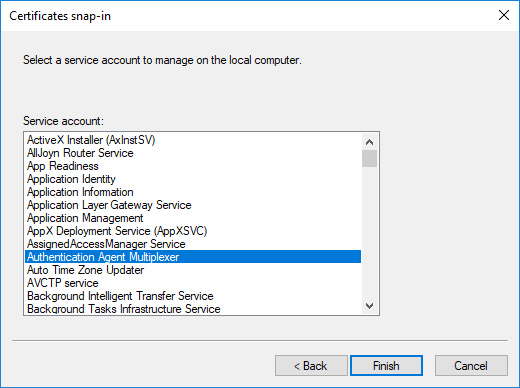
Select and click .
-
Select the service and click .
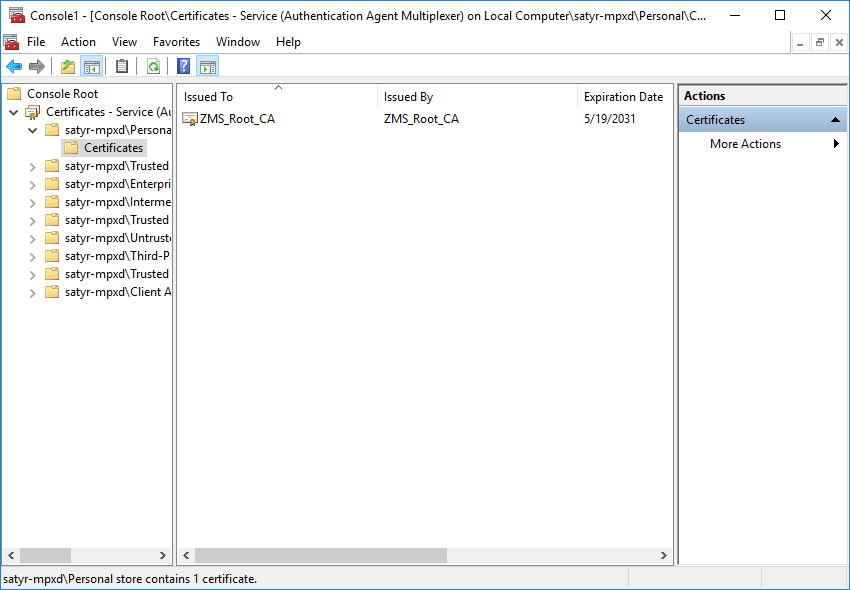
With the above steps a snap-in module has been configured that enables to conveniently manage the certificates related to the Zorp Authentication Agent Multiplexer.
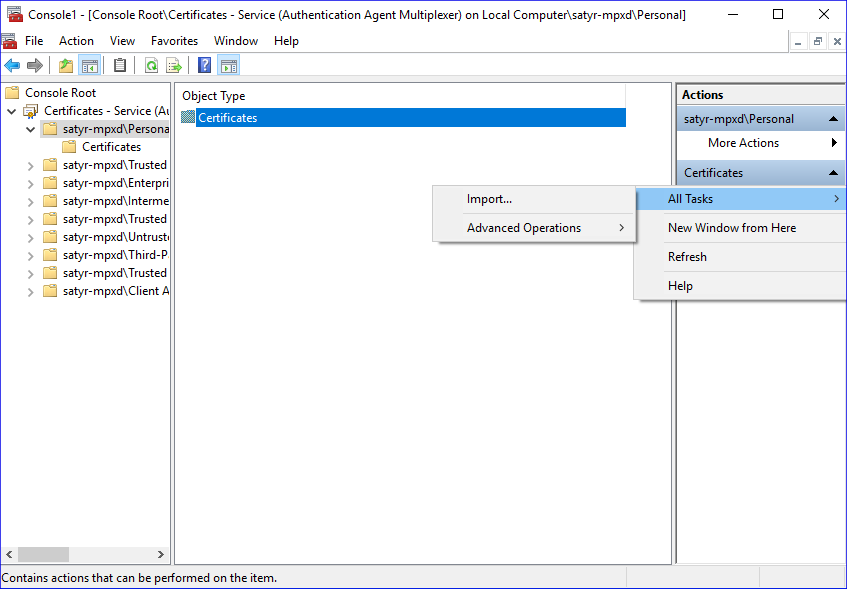
-
Navigate to , and click .
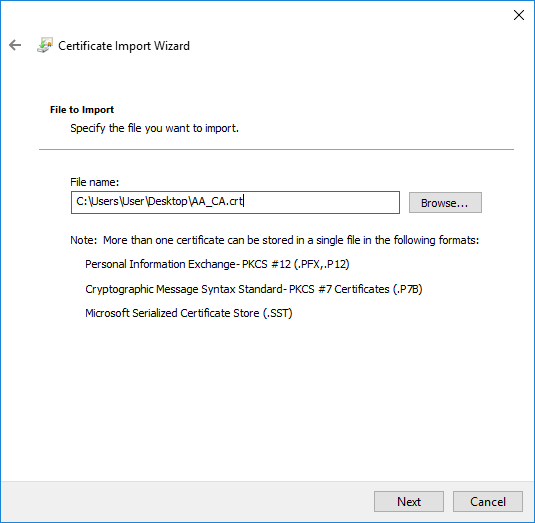
Right-click , navigate to . The is displayed. Click .
-
Select the certificate to import and click .
-
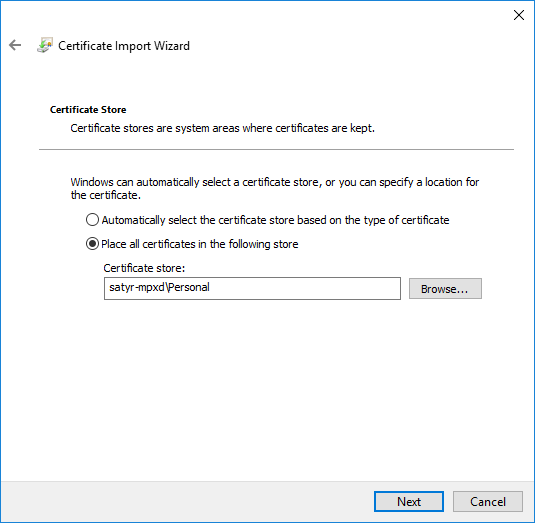
Click , when Windows offers a suitable certificate store by default.
-
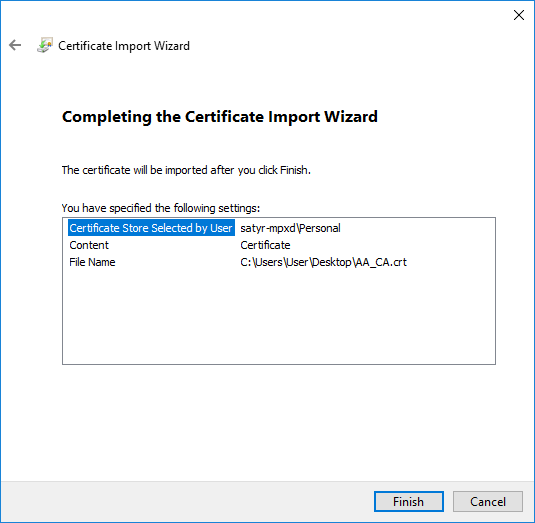
Click on the summary window and on the window that marks the successful import of the certificate.
The main window of MMC is displayed with the imported certificate.
-
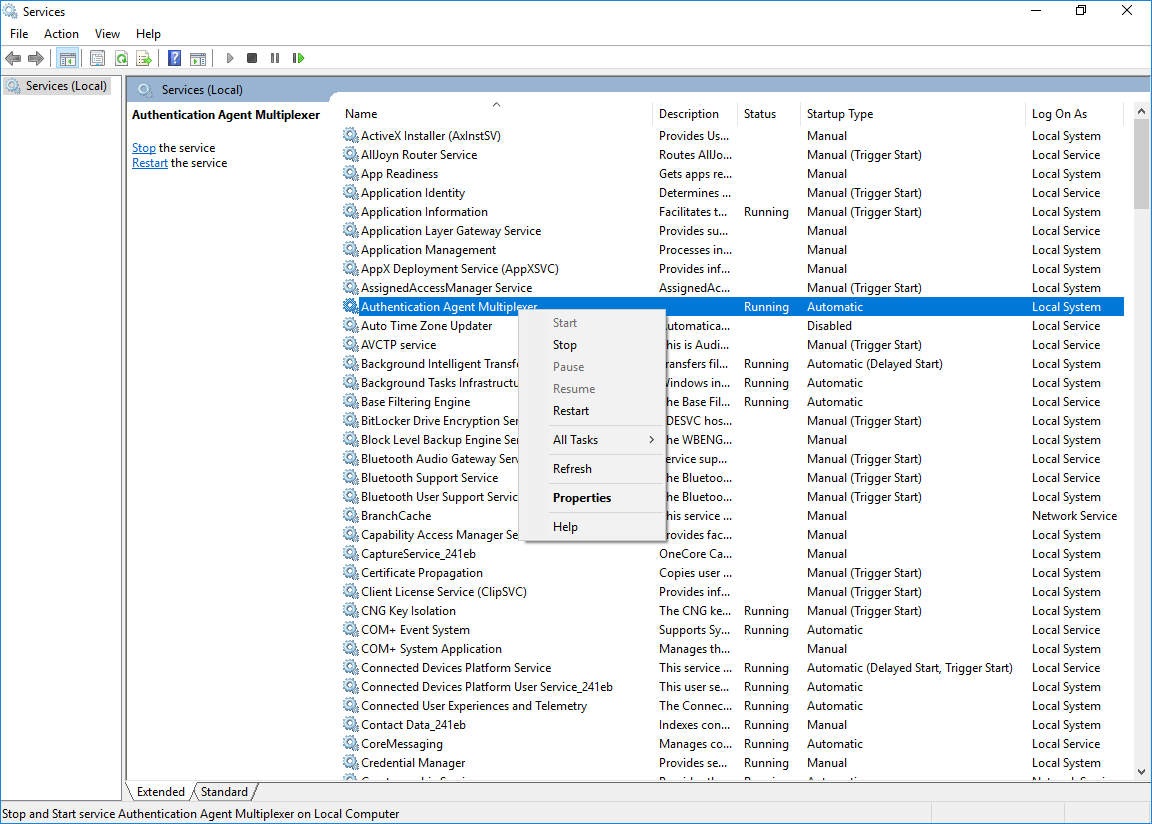
Restart the Zorp Authentication Agent service. Scroll to the Zorp Authentication Agent Multiplexer among the list of Services and right-click on it. Navigate to > .
It is also possible to start and stop the Zorp Authentication Agent here.
4.1.4. Procedure – Configuring X.509 certificate based authentication on Microsoft Windows platforms
Purpose:
For authentication based on X.509 certificates the certificate and the private key of the user has to be deployed onto the workstation. Import the certificate of the user into their personal certificate store. This can be accomplished most easily through the Control Panel item.:
Steps:
Click the button and type then press .
Navigate to > > .
-
Right-click and navigate to .
The is displayed.
Note Hardware keys and tokens having a suitable driver for Windows are also displayed in this store and can be used from the Zorp Authentication Agent.
Import the certificate, using the tool.
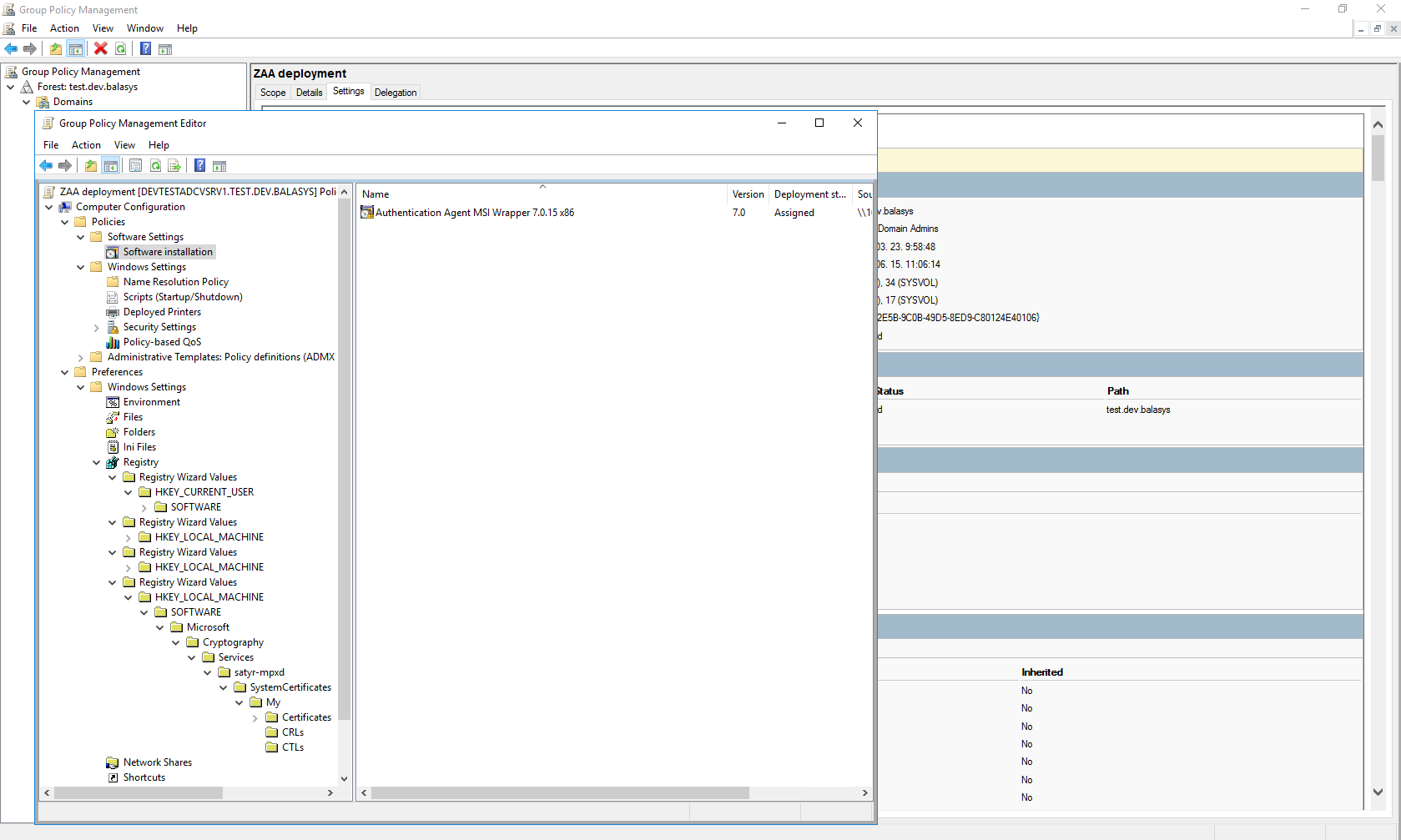
4.1.5. Procedure – Configuring Group Policy Object (GPO) deployment
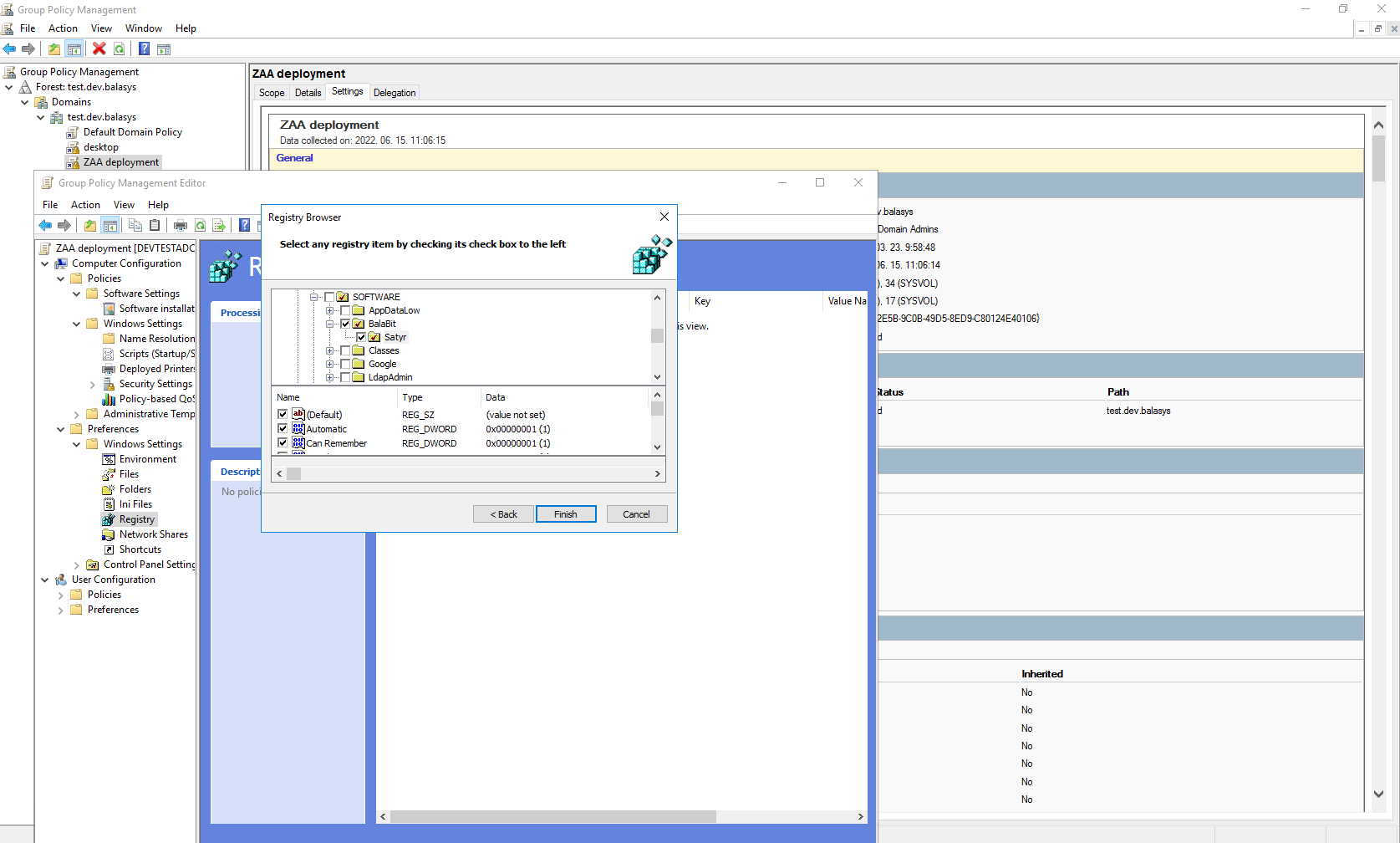
Import all four registry files to the GPO configurator system, so that the Registry Wizard can browse them. Later, remove the registry information if it is no longer required. If it is not possible to remove them, all four files have to be configured as registry keys.
Create a new policy to the corresponding forest as ZAA deployment.
Configure the corresponding parameters, as, for example, target scope or filtering and so on.
Edit the ZAA Deployment policy.
Add the ZAA msi installer as a new package under the path.
-
Browse the network share for the newly added package, select it, and set it to Auto installation.
-
Import all four registry settings with the help of the Registry Wizard. The HKLM registries under the path, and the HKCU registries under the path.
Close the GP editor.
The graphical client (satyr-gtk) has the following command line parameters:
- --help or -?
It displays a brief help message.
- --version or -V
It displays version number and compilation information.
- --automatic or -a
It enables automatic Kerberos authentication.
- --no-syslog or -l
It sends log messages to the standard output instead of syslog.
- --verbose <verbosity> or -v <verbosity>
It sets verbosity level to <verbosity>. The default verbosity level is
3; the possible values are0-10.- --logtags; or -T
It prepends log category and log level to each message.
Zorp Authentication Agent Multiplexer (satyr-mpxd) has the following command line parameters:
- --help or -?
It displays a brief help message.
- --version or -V
It displays the version number of satyr-mpxd.
- --no-syslog or -l
It sends log messages to the standard output instead of syslog.
- --verbose <verbosity> or -v <verbosity>
It sets verbosity level to <verbosity>. The default verbosity level is
3; possible values are0-10.- --logtags; or -T
It prepends log category and log level to each message.
- --aliasfile; or -a
It is the name (including full path) of a text file (for example,
/tmp/aliases) used by Zorp Authentication Agent Multiplexer to redirect the authentication requests of certain users to a different user in multiuser environments. For example, to redirect all authentication request of therootuser toMainUseradd the following line to the file:root: MainUser.- --log-spec; or -s
It sets verbosity mask on a per category basis. Each log message has an assigned multi-level category, where levels are separated by a dot. For example, HTTP requests are logged under http.request. The <spec> is a comma-separated list of log specifications. A single log specification consists of a wildcard matching log category, a colon, and a number specifying the verbosity level of that given category. The categories match from left to right, for example, --logspec 'http.*:5,core:3'. The last matching entry will be used as the verbosity of the given category. If no match is found the default verbosity specified with --verbose is used.
- --no-require-ssl; or -S
It turns off the SSL encryption of the communication between Zorp and the Multiplexer.
- --bind-address; or -b and, --bind-port; or -p
It is the IP address and the port, the Multiplexer is accepting connections on.
- --crt-dir; or -t
It is the path of the directory containing the certificate of the CA that issued the certificate of the Zorp firewall.
- --crl-dir; or -r
It is the path of the directory containing the Certificate Revocation List (CRL) related to the above CA.
To enable encryption between Zorp and the Zorp Authentication Agent complete the following steps. For the steps to be completed from ZMC, see Chapter 11, Key and certificate management in Zorp in Zorp Professional 7 Administrator Guide.
| Note |
|---|
During authentication, when Zorp communicates with ZAA, ZAA expects TLS-encrypted communication. In order to disable this and to use the communication without encryption (which is strongly against the recommendation, but useful for debugging purposes), the SSL encryption shall be disabled by setting the --no-require-ssl; or -S command line parameter. |
4.2.2.1. Procedure – Encrypting the communication between Zorp and the Zorp Authentication Agent on Linux platforms
Steps:
Create a CA (for example,
AA_CA) using the Zorp Management Console (ZMC). This CA will be used to sign the certificates shown by the Zorp firewalls to the Authentication Agents.Export the CA certificate into
PEMformat.-
Generate certificate request(s) for the Zorp firewall(s) and sign it with the CA created in Step 1.
Note Each firewall shall have its own certificate. Do not forget to set the firewall as the Owner host of the certificate.
Distribute the certificates to the firewalls.
-
Install the Zorp Authentication Agent (ZAA) application to the workstations and import to each machine the CA certificate exported in Step 2.
To import the CA certificate complete the following steps:
-
Create the
/etc/satyr/cadirectory:mkdir /etc/satyr/ca
Copy the certificate exported into
PEMformat in Step 2 into the/etc/satyr/cadirectory.-
Create symlinks to the certificate files:
c_rehash .
-
Restart the :
systemctl restart satyr-mpxd.service
The authentication client is now ready to accept encrypted connections from Zorp.
-
Create the appropriate outband authentication policies in ZMC and reference them among the services of Zorp. For details, see Chapter 15, Connection authentication and authorization in Zorp Professional 7 Administrator Guide.
For authentication based on X.509 certificates the certificate and the private key of the user has to be deployed onto the workstation. Create a directory called .satyr in the home folder of the user and copy the certificate and private key of the user in PEM format into this directory. Use the cert.pem and key.pem filenames, or create symlinks with these names pointing to the certificate and the key file. The Zorp Authentication Agent will automatically use the certificate found in this directory.
Purpose:
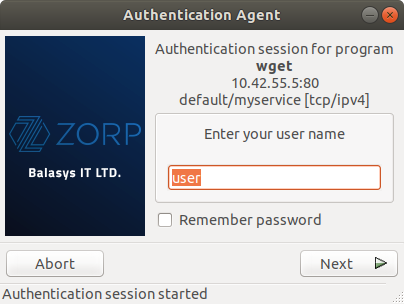
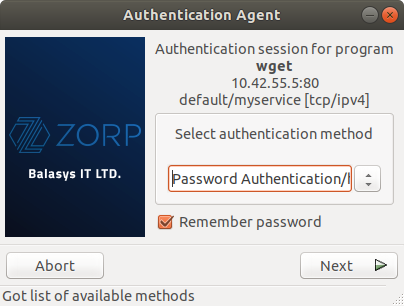
When the user launches an application that requires authentication (for example, a web browser, e-mail client, and so on) the Zorp firewall automatically displays the authentication client on the user's screen.
The client displays the name of the service requiring authentication (intra_http in the above example), and — provided that the administrator enabled it — further details of the connection (for example, destination IP address).
Steps:
-
To save your credentials so that the client will fill in the username and password automatically for later authentication attempts, select . For details on configuring password storage period length and deleting a previously saved password, see Procedure 6., .
To cancel the authentication at any time, click .
-
Enter your user name in the field and click .
-
Select the authentication method to use from the list. The list displays only the methods that are available for this user.
To authenticate with a password, select .
-
To use Kerberos authentication, select .
Note When using Kerberos authentication the authentication client is not displayed if you have configured in . For details, see Procedure 6., .
To authenticate with an X.509 certificate, select .
-
Provide the information required for the selected authentication method. For example, for , enter your password.
Note After successful authentication, the window of the authentication client is closed automatically, and the connection to the target server is established. If the authentication fails, the client displays an error message.
Purpose:
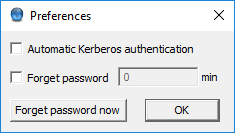
Zorp Authentication Agent is launched on desktop environment startup, and places its icon on the system tray. To configure Zorp Authentication Agent preferences, complete the following steps.
| Note |
|---|
To display the version number and other information about Zorp Authentication Agent, right-click the system tray icon and click . |
Steps:
-
Right-click the system tray icon and click .
To enable automatic Kerberos authentication without user interaction with the Zorp Authentication Agent, select . In this case, Zorp Authentication Agent will use the username provided during Windows or Linux desktop session login.
To prevent unauthorized initiation of network connections through unattended machines, configure . Enter the number of minutes after which Zorp Authentication Agent deletes the stored password and requires authentication for new connection requests.
-
To immediately delete the stored password from the Zorp Authentication Agent and require authentication for new connection requests, click .
ZAA stores its preferences in the ~/.config/aa/aa.cfg configuration file on Linux, and in the Windows Registry on Microsoft Windows platforms, for more information see Section 4.1.1, Registry entries on Microsoft Windows platforms.
To start or stop Zorp Authentication Agent, perform one of the following steps.
To stop Zorp Authentication Agent, right-click the system tray icon and click .
To restart the Zorp Authentication Agent select the button, type and then press .